Cisco ISE Administrator Accounts: CLI and GUI Access
Introduction
During the installation of an ISE node, whether virtualized or deployed on a physical SNS appliance, an initial administrator account must be created. This account is subsequently used to generate two distinct user identities: one for Command Line Interface (CLI) access and one for Graphical User Interface (GUI) access. These accounts are specifically intended for administering and managing the ISE environment.
1Enter hostname[]: IT-PSN-04-EVENG
2Enter IP address[]: X.X.X.X
3Enter IP netmask[]: X.X.X.X
4Enter IP default gateway[]: X.X.X.X
5Do you want to configure IPv6 address? Y/N [N]: N
6Enter default DNS domain[]: domain.name
7Enter primary nameserver[]: X.X.X.X
8Add secondary nameserver? Y/N [N]: N
9Enter NTP server [time.nist.gov]: ntp.name
10Add another NTP server? Y/N [N]: N
11Enter system timezone [UTC]: CET
12Enable SSH service? Y/N [N]: Y
13Enter username [admin]: adminstup
14Enter password:
15Enter password again:
16Bringing up network interface...
17[OUTPUT OMITTED]The GUI account provides access to the web interface, offering a comprehensive view of the ISE deployment, with visibility tailored to the deployment type and in distributed environments to the specific role of each node. The CLI account, on the other hand, is primarily used to access ISE nodes via SSH. Initially, both accounts share the same credentials, allowing the same username and password to be used for authentication on both interfaces. More precisely, the CLI account created during the setup phase is copied into the local store used by the GUI (this is the only case in which this type of copy occurs). This behavior is confirmed by the logs generated during the installation phase, as shown below.
1Copying first CLI user to be first ISE admin GUI user...As we will see in this post, ISE uses a Role-Based Access Control (RBAC) model to categorize users by responsibility, defining both the scope of their actions and their level of visibility. For each access method, administrators can configure, with fine-grained control, which commands or menus a user may access and which data they are allowed to view. By default, the CLI account created during the initial installation is assigned the Admin role, while the corresponding GUI account belongs to the Super Admin group.
In general, the roles available depend on the access method: the CLI supports only two predefined roles, whereas the GUI provides a broader set of built-in groups and allows the creation of custom groups to meet specific operational requirements.
CLI Access and Privileges
CLI access to ISE can be achieved through multiple methods:
- Local access through the console port
- Remote connection over SSH
- Remote connection through the Cisco Integrated Management Controller (CIMC)
Two types of user accounts are available for CLI access: Admin and User, each granting a distinct set of privileges. The Admin account provides elevated privileges for system-level operations, including:
- Start and stop the ISE application
- Apply software patches and upgrades
- Reload or shut down the ISE appliance
- View all system and application logs
When logged in with an Admin account, a wide range of commands is available, as shown below.
1IT-PSN-04-EVENG/adminstup#?
2Possible completions:
3 application Application Install and Administration
4 backup Backup system
5 backup-logs Backup system and application logs
6 clear Reset functions
7 clock Set the System Clock
8 configure cfg
9 copy Enter URL (use disk:/path/file for local) (Max Size - 2048)
10 crypto Crypto operations
11 debug Debugging functions (see also 'undebug')
12 delete Delete a file
13 dir List files on local filesystem
14 esr Enter the Embedded Services Router console
15 exit Exit the management session
16 forceout Force Logout all the sessions of a specific system user
17 generate-password Username for which password has to be generated
18 halt Shutdown the system
19 idle-timeout Idle timeout for all the sessions of a specific system user
20 license License operations
21 mkdir Create new directory
22 nslookup DNS lookup for an IP address or hostname
23 password Update Password
24 patch Install System or Application Patch
25 permit List cli for Secure Tunnel
26 ping Ping a remote ip address
27 ping6 Ping a remote ipv6 address
28 reload Reload the system
29 reset-config Reset network and time settings
30 restore Restore system
31 rmdir Remove existing directory
32 screen-length Configure screen length
33 screen-width Configure screen width
34 show Show information about the system
35 ssh SSH to a remote ip address
36 tech TAC commands
37 terminal Set terminal line parameters
38 traceroute Trace the route to a remote ip address
39 undebug Disable debugging functions (see also 'debug')
40 who Display currently logged on usersThe show command, in particular, grants access to the following system sections.
1IT-PSN-04-EVENG/adminstup#show ?
2Possible completions:
3 application Display application(s) information
4 backup Show backup information
5 banner Show login banners
6 cdp CDP show commands
7 clock Show clock information
8 container Show container information
9 cpu Display CPU information
10 crypto Display Crypto operations
11 disks Display disk and filesystem information
12 esr Show Embedded Services Router information
13 firewall Show firewall rules
14 history Display CLI command history
15 icmp_status Display icmp echo response configuration information
16 interface Display interface info
17 inventory Display hardware inventory information
18 ip Show IP info
19 ipv6 Show IPv6 info
20 logging Display system logging information
21 logins List login history
22 memory Display memory information
23 ntp Show NTP servers
24 ports Display all processes listening on open ports
25 process Display system processes
26 repository Show repository contents
27 restore Show restore information
28 running-config Display current configuration
29 snmp-server Show snmp-server information
30 tech-support Show tech-support details
31 terminal Display terminal configuration parameters
32 timezone Show timezone
33 timezones Show timezones
34 udi Show udi information
35 uptime Display system uptime
36 users Display logged-in users information
37 version Show version infoThe second type of CLI user is the User account, which has limited privileges. Consequently, it cannot perform configuration changes or monitor the status of ISE application processes, and is restricted to a subset of basic operational commands, as illustrated below.
1IT-PSN-04-EVENG/userAcn#?
2Possible completions:
3 crypto Crypto operations
4 exit Exit the management session
5 license License operations
6 nslookup DNS lookup for an IP address or hostname
7 password Update Password
8 ping Ping a remote ip address
9 ping6 Ping a remote ipv6 address
10 show Show information about the system
11 terminal Set terminal line parameters
12 traceroute Trace the route to a remote ip addressThis limitation also applies to the information accessible via the show command.
1IT-PSN-04-EVENG/userAcn#show ?
2Possible completions:
3 cdp CDP show commands
4 clock Show clock information
5 cpu Display CPU information
6 crypto Display Crypto operations
7 disks Display disk and filesystem information
8 icmp_status Display icmp echo response configuration information
9 interface Display interface info
10 inventory Display hardware inventory information
11 logins List login history
12 memory Display memory information
13 ntp Show NTP servers
14 ports Display all processes listening on open ports
15 process Display system processes
16 terminal Display terminal configuration parameters
17 timezone Show timezone
18 udi Show udi information
19 uptime Display system uptime
20 version Show version infoCLI Account Creation
Local CLI accounts can be created by entering configuration mode and executing the following command.
1IT-PSN-04-EVENG/adminstup(config)#username <user-name> password <plain | hash> <password> role <admin | user> email <user-email> <disabled>The parameters that must be specified are:
- Username: The name associated with the account being created. During the initial ISE configuration, the Admin account is assigned the default name admin
- Password: The password associated with the account. It can be provided either in plain text or as a hash. When entering a plain-text password, characters such as "!" and "#" must be escaped with a backslash. In the running configuration, the password is automatically displayed as a SHA-256 hash
- Role: The type of role assigned to the user, either Admin or User
Other parameters that can be specified include:
- Email: Associates an email address with the account. This value can be used to notify the user when their password is approaching expiration, provided the feature is enabled and properly configured
- Disabled: Creates the account in a disabled state, meaning it cannot be used until explicitly enabled
To guarantee that a password meets the required policy on the first attempt, the generate-password <user-name> command can be used to generate a compliant password, as illustrated in the example below.
1IT-PSN-04-EVENG/adminstup#generate-password userTest
2cP2o2Z#v
3IT-PSN-04-EVENG/adminstup#generate-password userTest
4W7tXMAVmThe generated password should then be used within the username command. Note that each time the command is used for the same username, a different password is generated.
Once an account has been created, all locally configured CLI accounts, along with their respective statuses, can be verified using the show users status command, as illustrated in the example below. The verification of users created and used on this node will be discussed in the next section.
1IT-PSN-04-EVENG/adminstup#show users status
2
3USERNAME ROLE DISABLED LOCKED
4adminstup Admin
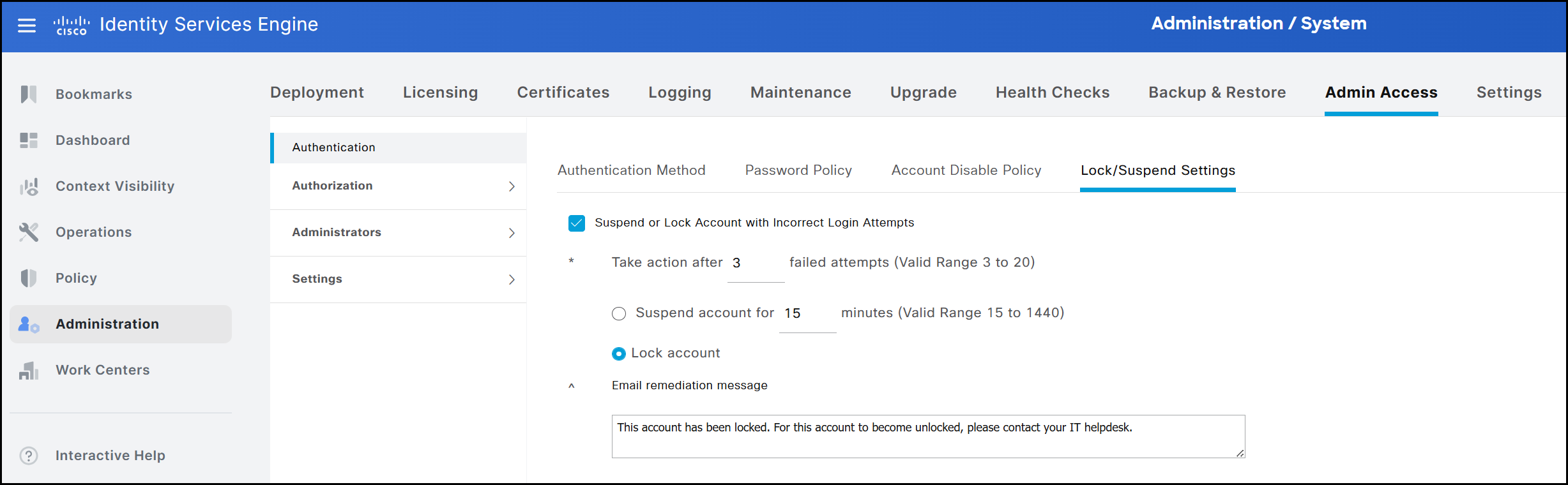
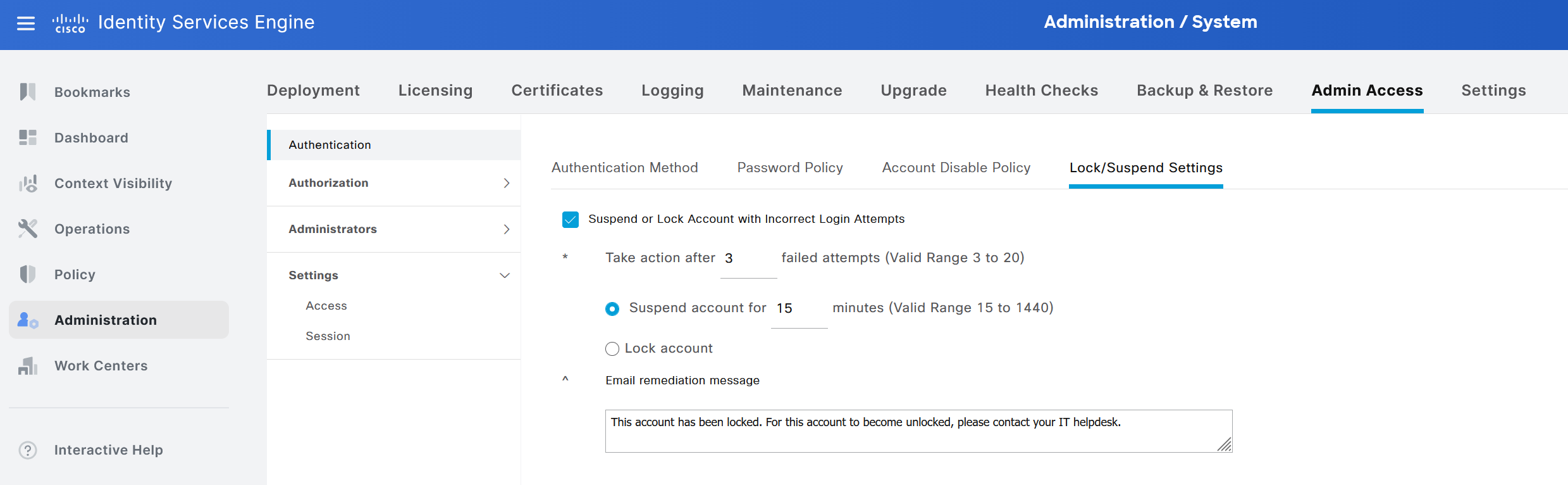
5userAcn User The previous output indicates that, in addition to the Disabled state, a Locked state can also be applied to an account. In the scenario shown in the following figure, if a user attempts to log in multiple times with an incorrect password (three attempts in this example), the CLI account is automatically locked. While rebooting the node could unlock the account, this would require a scheduled maintenance window in a production environment. Consequently, it is preferable to rely on the temporary suspension mechanism, which locks the account for a defined period (15 minutes in this example) before it automatically becomes available again.
For example, the output below illustrates the result when the user userAcn attempts to log in three consecutive times with an incorrect password.
1IT-PSN-04-EVENG/adminstup#show users status
2
3USERNAME ROLE DISABLED LOCKED
4adminstup Admin
5userAcn User *The difference between Disabled and Locked modes in the CLI can be clearly verified using the show running-config password-policy command. When the Suspend account for X minutes option is selected in the GUI, the running configuration includes the password-lock-timeout 15 entry. Conversely, if the Lock account option is selected, this entry is absent from the configuration. By default, on ISE 3.4, the Suspend... option is selected.
1IT-PSN-04-EVENG/adminstup#show running-config password-policy | include password-lock
2 password-lock-enabled
3 password-lock-retry-count 3
4 password-lock-timeout 15The settings above are included in ISE’s password policies and will be covered in detail later.
As with accounts created through the CLI, internal administrator accounts created via the GUI can also be viewed. To do this, ISE configuration mode must be accessed by entering the application configure ise command from EXEC mode. The following lists all options available to the Admin CLI users; for the context of this guide, option 15 is the relevant selection.
1IT-PSN-04-EVENG/adminstup#application configure ise
2
3Selection configuration option
4[1]Reset M&T Session Database
5[2]Rebuild M&T Unusable Indexes
6[3]Purge M&T Operational Data
7[4]Reset M&T Database
8[5]Refresh Database Statistics
9[6]Display Profiler Statistics
10[7]Export Internal CA Store
11[8]Import Internal CA Store
12[9]Create Missing Config Indexes
13[10]Create Missing M&T Indexes
14[12]Generate Daily KPM Stats
15[13]Generate KPM Stats for last 8 Weeks
16[14]Enable/Disable Counter Attribute Collection
17[15]View Admin Users
18[16]Get all Endpoints
19[19]Establish Trust with controller
20[20]Reset Context Visibility
21[21]Synchronize Context Visibility With Database
22[22]Generate Heap Dump
23[23]Generate Thread Dump
24[24]Force Backup Cancellation
25[25]CleanUp ESR 5921 IOS Crash Info Files
26[26]Recreate undotablespace
27[27]Reset Upgrade Tables
28[28]Recreate Temp tablespace
29[29]Clear Sysaux tablespace
30[30]Fetch SGA/PGA Memory usage
31[31]Generate Self-Signed Admin Certificate
32[32]View Certificates in NSSDB or CA_NSSDB
33[33]Recreate REPLOGNS tablespace
34[34]View Native IPSec status
35[35]Enable/Disable/Current_status of Audit-Session-ID Uniqueness
36[36]Check and Repair Filesystem
37[37]Enable/Disable/Current_status of RSA_PSS signature for EAP-TLS
38[0]ExitBy entering 15 and pressing Enter, the following output is displayed.
1Admin User Report
2
3User Name Description Enabled First Name Last Name Email Groups
4=============== ==================== ======== =============== =============== ========================= ========================================
5ERSGUIOper ENABLED ["ERS Operator"]
6
7adminstup Default Admin User ENABLED ["Super Admin"]
8
9testGUI ENABLED ["Super Admin"]Note the adminstup account, which was configured at the CLI level and then copied into the GUI. After creating an account via CLI, it is possible to verify the operation in the logs using the command show logging system ade/ADE.log | include 1018.
12026-03-23T21:58:41.022362+01:00 IT-PSN-04-EVENG CARSSetup[3021]: ADEAUDIT 1018, type=USER, name=USER CONFIGURATION MODIFIED, username=adminstup, cause=CLI User configuration has been modified, adminipaddress=192.168.0.1, interface=CLI, detail=Added user userAcn with role: User state: Enabled successfullyThe output displays a log entry containing several details about the newly created account, excluding the password. The information is presented in the following order:
- Log ID, which in this case is 1018
- Description of the logged event, in this case USER CONFIGURATION MODIFIED
- Administrator account that performed the action, adminstup in this example
- IP address from which the administrator was connected when creating the user, in this case 192.168.0.1
- Type of account that was created, shown in the detail field (here, a User account)
- State associated with the account, which in this example is enabled. Using the disabled keyword creates an account in a non-enabled state, making it temporarily unavailable
The same event can also be verified in an alternative log file (ise-psc.log), with an example output shown below.
12026-03-23 21:58:41,418 INFO [AdeSyslogProcessor][[]] cpm.infrastructure.systemconfig.syslogproc.AdeSyslogContent -:::::- SCH: InfraTCPMessage: msg: InfraUdpMessage: <130>Mar 23 21:58:41 IT-PSN-04-EVENG CARSSetup[3021]: ADEAUDIT 1018, type=USER, name=USER CONFIGURATION MODIFIED, username=adminstup, cause=CLI User configuration has been modified, adminipaddress=192.168.0.1, interface=CLI, detail=Added user userAcn with role: User state: Enabled successfullyStarting with ISE Release 3.3, any user account created via the CLI is required to change its password at first login. The corresponding output is shown below.
1login as: userAcn
2userAcn@10.0.0.1's password:
3Pre-authentication banner message from server:
4| You are required to change your password immediately (administrator enforced)
5> .
6End of banner message from server
7You are required to change your password immediately (administrator enforced).
8WARNING: Your password has expired.
9You must change your password now and login again!
10Changing password for user userAcn.
11Current password:
12New password:
13Retype new password:Once the new password is entered and confirmed, the session is terminated. At the next login, the same user account, userAcn, can be used along with the newly configured password. It is also useful to examine how the node behaves when a user sets a new password. The following logs illustrate this process.
12026-03-23T22:03:50.867979+01:00 IT-PSN-04-EVENG CARSSetup[3021]: ADEAUDIT 1018, type=USER, name=USER CONFIGURATION MODIFIED, username=system, cause=CLI User configuration has been modified, adminipaddress=127.0.0.1, interface=CLI, detail=User userAcn has been modified with password, role: User state: Enabled successfullyUnlike the previous example, the username and adminipaddress fields are different. In this case, they are populated with system and 127.0.0.1, which corresponds to the local address of the machine. This occurs because the update is triggered internally by ISE itself. In general, following the creation of an account, whether Admin or User, its password can be changed at any time. A password reset can be performed either directly by the user or by an administrator. For a User account, the password can be reset using the password command from EXEC mode. For an Admin account, the password can be reset not only using the previous method, but also by using the username... command in configuration mode and specifying the new password accordingly.
Administrators can modify or delete any account, regardless of role. The recommended procedure for removing an account is as follows:
- Execute the command show running-config username and copy the entry corresponding to the account to be removed
- Enter configuration mode and issue the same command using the negated form (i.e., no username...) This operation is not available to User-level accounts, as access to configuration mode is restricted.
CLI Account Verification
With multiple accounts configured, an administrator may want to review the most recent CLI access attempts on ISE. This can be done using the show logins cli command, which by default displays the last 10 recorded entries. If needed, additional results can be shown by specifying a higher value with show logins cli count <entries-number>.
1IT-PSN-04-EVENG/adminstup#show logins cli
2userAcn pts/1 192.168.0.1 Tue Mar 24 08:01 still logged in
3userAcn pts/1 192.168.0.1 Tue Mar 24 07:56 - 07:56 (00:00)
4adminstu pts/0 192.168.0.1 Tue Mar 24 07:47 still logged in
5adminstu pts/0 192.168.0.1 Mon Mar 23 22:34 - 23:16 (00:42)
6reboot system boot 4.18.0-513.18.1. Mon Mar 23 22:32 still running
7userAcn pts/1 192.168.0.1 Mon Mar 23 22:04 - 22:23 (00:19)
8userAcn pts/1 192.168.0.1 Mon Mar 23 22:03 - 22:03 (00:00)
9userAcn pts/1 192.168.0.1 Mon Mar 23 22:01 - 22:02 (00:00)
10userAcn pts/1 192.168.0.1 Mon Mar 23 22:00 - 22:01 (00:00)
11userAcn pts/1 192.168.0.1 Mon Mar 23 21:59 - 22:00 (00:00)
12
13wtmp begins Thu Aug 1 16:17:38 2024To verify which users are currently connected, the show users command can be used. An example of the output is shown below.
1IT-PSN-04-EVENG/adminstup#show users
2
3USERNAME ROLE HOST TTY LOGIN DATETIME
4
5adminstup Admin 192.168.0.1 pts/0 Tue Mar 24 07:47:11 2026
6
7userAcn User 192.168.0.1 pts/1 Tue Mar 24 08:01:47 2026
8
9-------------------
10DETACHED SESSIONS:
11-------------------
12
13USERNAME ROLE STARTDATE
14
15% No disonnected user sessions presentAnother command available for the same purpose is who. As shown below, the output format is slightly different. In addition to displaying the username, source IP address, and protocol used, it also allows to verify the mode in which the user is currently operating. For example, in the output below, the user adminstup is currently in operational mode (i.e., EXEC mode). If the user were in configuration mode, it would be displayed as config-terminal.
1IT-PSN-04-EVENG/adminstup#who
2Session User Context From Proto Date Mode
3 1797 userAcn cli 192.168.0.1 ssh 08:01:47 operational
4*1793 adminstup cli 192.168.0.1 ssh 07:47:11 operationalIf an Admin user attempts to delete an account that is currently in an active session, the operation will fail, and the following message will be displayed.
1IT-PSN-04-EVENG/adminstup(config)#no username userAcn password hash $6$B2Yr7noh.XRzNA5.$1Yl/fQ2Lo8uq7U861Wro7CgoMqm0Q2isv0nDUpqVj7kmZQLIAEyde8kCIUyRWfvKJ24d91nnWMchfP39LQ7Nd0 role user
2% Error: Cannot delete user while active session exist. Use 'forceout' CLI to remove active session of the user.If it becomes necessary to forcibly terminate the session of a specific user who is currently active and appears in the previous output, the command forceout <user-name> can be used. The log generated by executing the forceout userAcn command is shown below.
12026-03-24T08:10:35.924925+01:00 IT-PSN-04-EVENG CARSSetup[1319852]: ADEAUDIT 2040, type=FORCEOUT, name=FORCEOUT USER, username=system, cause=Forced logout of all the sessions of a CLI user, adminipaddress=127.0.0.1, interface=CLI, detail=Forced logout of user userAcn successful
22026-03-24T08:10:35.864495+01:00 IT-PSN-04-EVENG ADE-SERVICE[1320]: [1319852]:[info] user: user.c[3319] [system]: Invoked force logout for user: userAcn
32026-03-24T08:10:35.909279+01:00 IT-PSN-04-EVENG ADE-SERVICE[1320]: [1319852]:[info] user: user.c[3355] [system]: force logout: CLI user found a match userAcn
42026-03-24T08:10:35.924771+01:00 IT-PSN-04-EVENG ADE-SERVICE[1320]: [1319852]:[info] user: user.c[3395] [system]: Force logout on userAcn successfulThe user whose session is forcibly terminated will receive a message such as Remote side unexpectedly closed network connection.
In this case, the log ID differs from the previous example, changing from 1018 to 2040. The log also specifies the username that was forcibly logged out, shown in the detail field. As in the previous scenario, the adminipaddress field corresponds to the local address of the node. While an Admin-level user can forcibly terminate the session of another user, whether Admin or User, a User-level account cannot force any session termination, as the required command is not available.
In addition to runtime display commands and the show user status command, the generic show running-config username command can be used to view all locally created users directly from the configuration. An example of the output is shown below.
1IT-PSN-04-EVENG/adminstup#show running-config username
2username adminstup password hash $6$YGfde6xAYCz6kzZT$AlzvVwID0HStyAuxLkK5BS7mYgXaQLFDmqd75lMXi6a163vxRj.U.UdUh9OFzSTFzPM4wISPQeAWpW9f7SYQi. role admin
3username userAcn password hash $6$B2Yr7noh.XRzNA5.$1Yl/fQ2Lo8uq7U861Wro7CgoMqm0Q2isv0nDUpqVj7kmZQLIAEyde8kCIUyRWfvKJ24d91nnWMchfP39LQ7Nd0 role userAdditional options are available to further refine the search:
1IT-PSN-04-EVENG/adminstup#show running-config username ?
2Possible completions:
3 adminstup Username (Max Size - 31)
4 userAcn Username (Max Size - 31)
5 | Output modifiers
6 <cr>
7Possible match completions:
8 disabled User is disabled
9 email User email address
10 password Password and user role
11 role Specify user roleCLI Account Password Policy
As demonstrated earlier, creating a local user account from the CLI is a straightforward process. One of the most critical attributes of any account is its password. To strengthen overall security, ISE enforces a set of password policies that must be followed when defining a password. These policies can be reviewed using the show running-config password-policy command. An example of the output is provided below.
1IT-PSN-04-EVENG/adminstup#show running-config password-policy
2password-policy
3 digit-required
4 lower-case-required
5 min-password-length 8
6 no-username
7 password-expiration-days 45
8 password-expiration-enabled
9 password-lock-enabled
10 password-lock-retry-count 3
11 password-lock-timeout 15
12 upper-case-required
13!Contrary to what might be assumed, these policies are read-only when accessed from the CLI. Any modifications must be performed through the GUI. Attempting to make changes from the CLI results in the following error message.
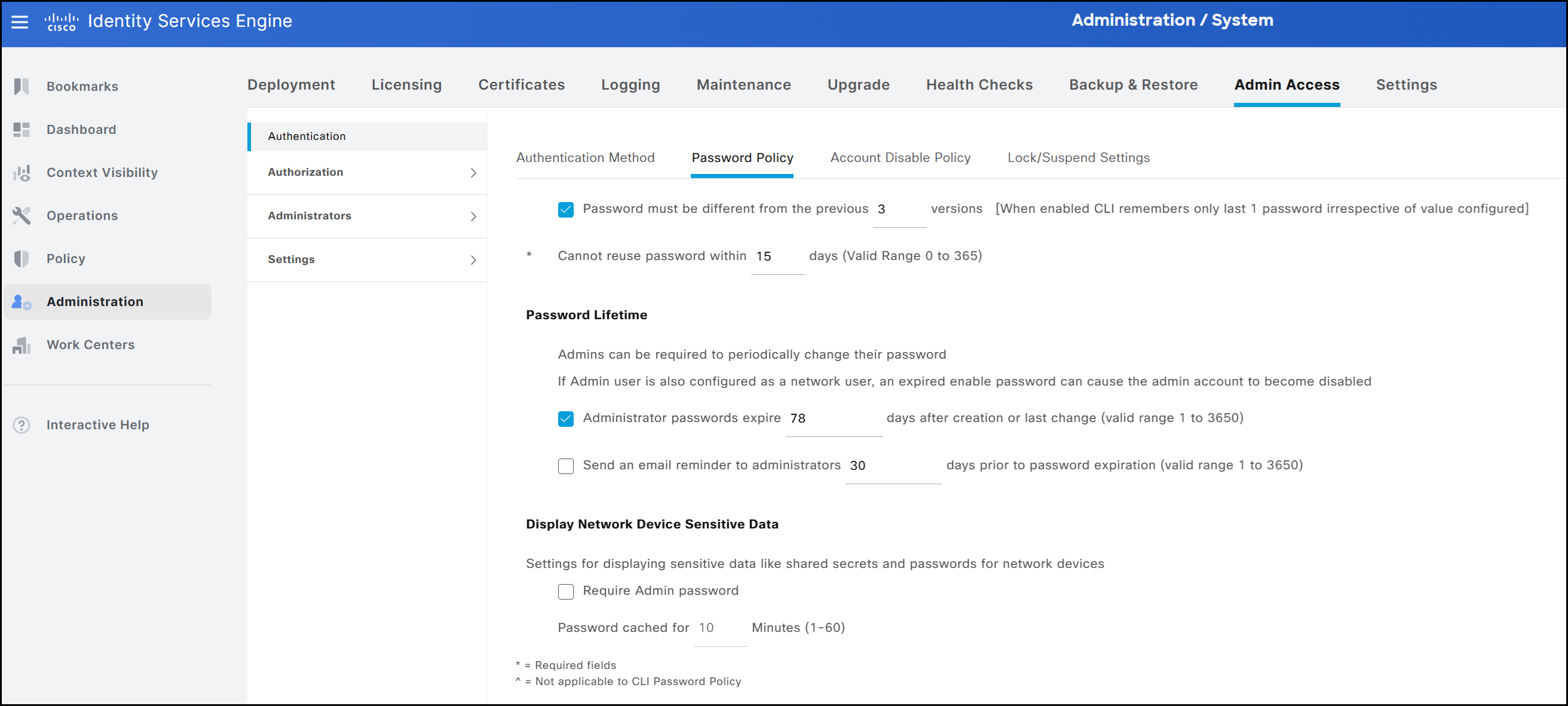
1IT-PSN-04-EVENG/adminstup(config-password-policy)#password-expiration-days 12
2% Error: Configuration changes ignored. Password policy is replicated from ISE administration node. Please set CLI password policy using the ISE web UI on the primary administration node.Therefore, all changes to password policies must be performed from the GUI using an administrator-level account, such as Super Admin or System Admin. It should be noted that not all GUI configuration options apply to accounts created via the CLI (for instance, the policy Password must not contain → This word or any of its characters in reverse order). The configuration menu for password policies can be found under Administration → System → Admin Access → Authentication → Password Policy. For policies applied to accounts created through the CLI, any modifications are automatically reflected in the corresponding CLI output. For example, if the maximum password lifetime is changed from its default value to a custom setting, such as 78 days, this updated value will also appear in the CLI output, as shown below.
1IT-PSN-04-EVENG/adminstup(config-password-policy)#do show running-config password-policy
2password-policy
3 digit-required
4 lower-case-required
5 min-password-length 8
6 no-username
7 password-expiration-days 78
8 password-expiration-enabled
9 password-lock-enabled
10 password-lock-retry-count 3
11 password-lock-timeout 15
12 upper-case-required
13!Having reviewed the creation, management, and monitoring of accounts via the CLI, the next section examines these same operations from the GUI perspective.
GUI Access and Privileges
The second, and most frequently used, method for managing ISE is through the GUI. From there, administrators can:
- Manage deployments, help desk operations, network devices, and node monitoring and troubleshooting
- Manage ISE services, policies, administrator accounts, and overall system configuration and operations
- Change administrator and user passwords
GUI Account Creation
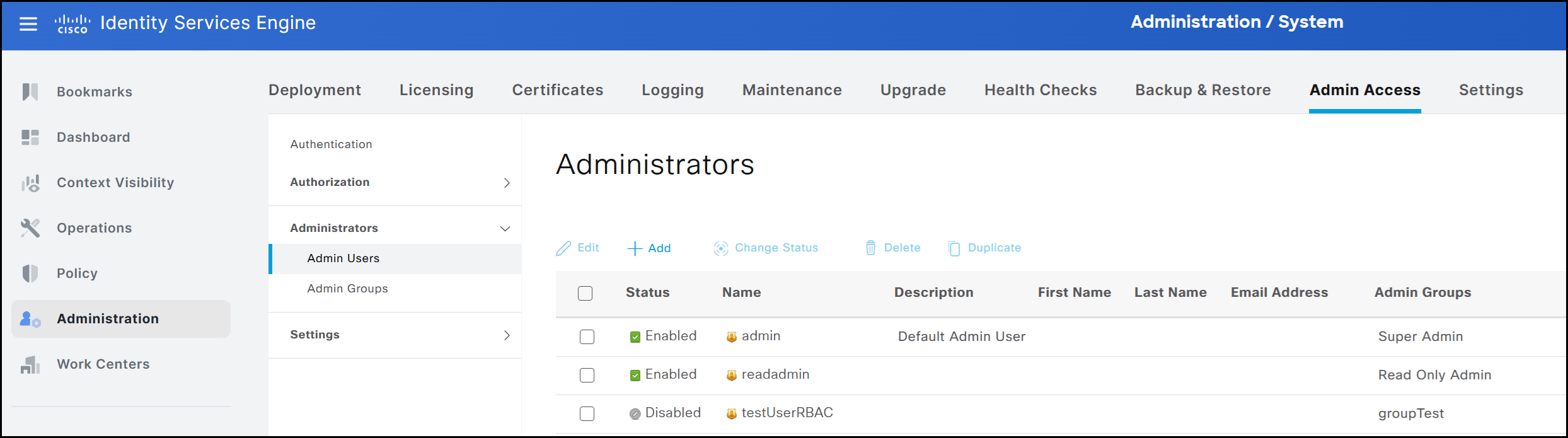
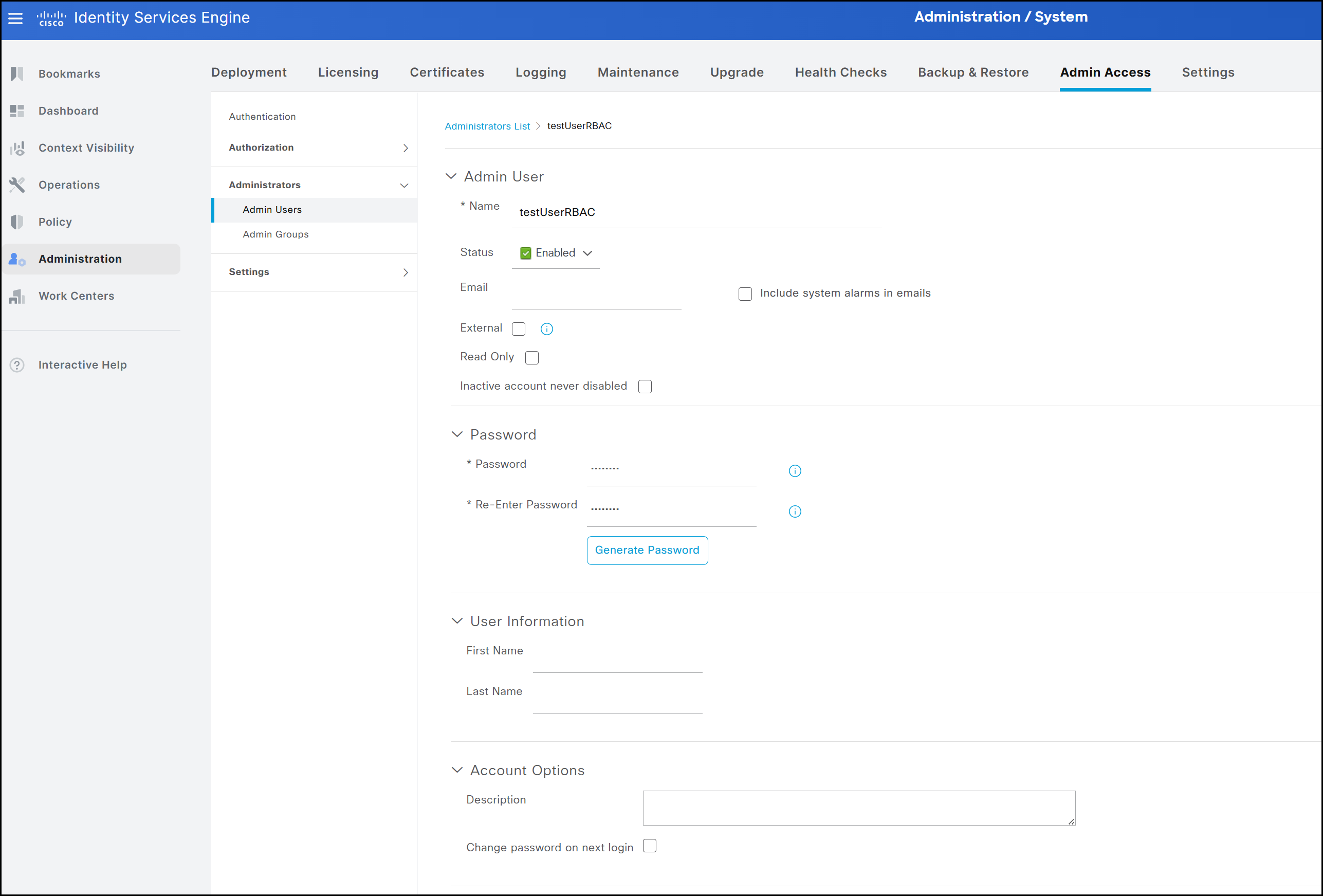
Administrator accounts can be managed under Administration → System → Admin Access → Administrators → Admin Users. From this page, new accounts can be created and all available attributes can be assigned to them.
Below are the logs related to the configuration of a new user via the GUI.
12026-03-24 08:39:17,059 INFO [admin-http-pool5][[]] cisco.ise.ups.internaluser.InternalUserAdapter -::adminstup:::- Going to validate and set new password
22026-03-24 08:39:17,067 INFO [admin-http-pool5][[]] cisco.ise.ups.internaluser.InternalUserServiceImpl -::adminstup:::- going to save test_GUI_Account
32026-03-24 08:39:17,067 INFO [admin-http-pool5][[]] cisco.ise.ups.internaluser.InternalUserServiceImpl -::adminstup:::- done validation for user test_GUI_Account
42026-03-24 08:39:17,067 INFO [admin-http-pool5][[]] cisco.ise.ups.internaluser.InternalUserServiceImpl -::adminstup:::- retrieved RBAC groups for user test_GUI_Account. number of groups: 1
52026-03-24 08:39:17,077 INFO [admin-http-pool5][[]] cisco.ise.ups.internaluser.InternalUserServiceImpl -::adminstup:::- Going to persist user test_GUI_Account
62026-03-24 08:39:17,082 INFO [admin-http-pool5][[]] cisco.ise.ups.internaluser.InternalUserServiceImpl -::adminstup:::- Successfully persisted user test_GUI_Account
72026-03-24 08:39:17,084 INFO [admin-http-pool5][[]] cisco.ise.ups.internaluser.InternalUserServiceImpl -::adminstup:::- Sent audit for user test_GUI_AccountIn addition to creating users, the same interface allows them to be deleted or disabled. When a user is disabled, any attempt to log in with the associated credentials will be denied access to the ISE GUI. It is important to note that these users are stored internally within the ISE cluster. Unlike CLI-created users, GUI-based users can access the graphical interface of each node in a distributed deployment.
Particular attention should be given to the administrator account created during the initial setup. This account cannot be deleted or disabled, unlike the default CLI account, which can be removed. Consequently, only a limited subset of its attributes can be modified. The figure below shows all configurable attributes for each administrator account.
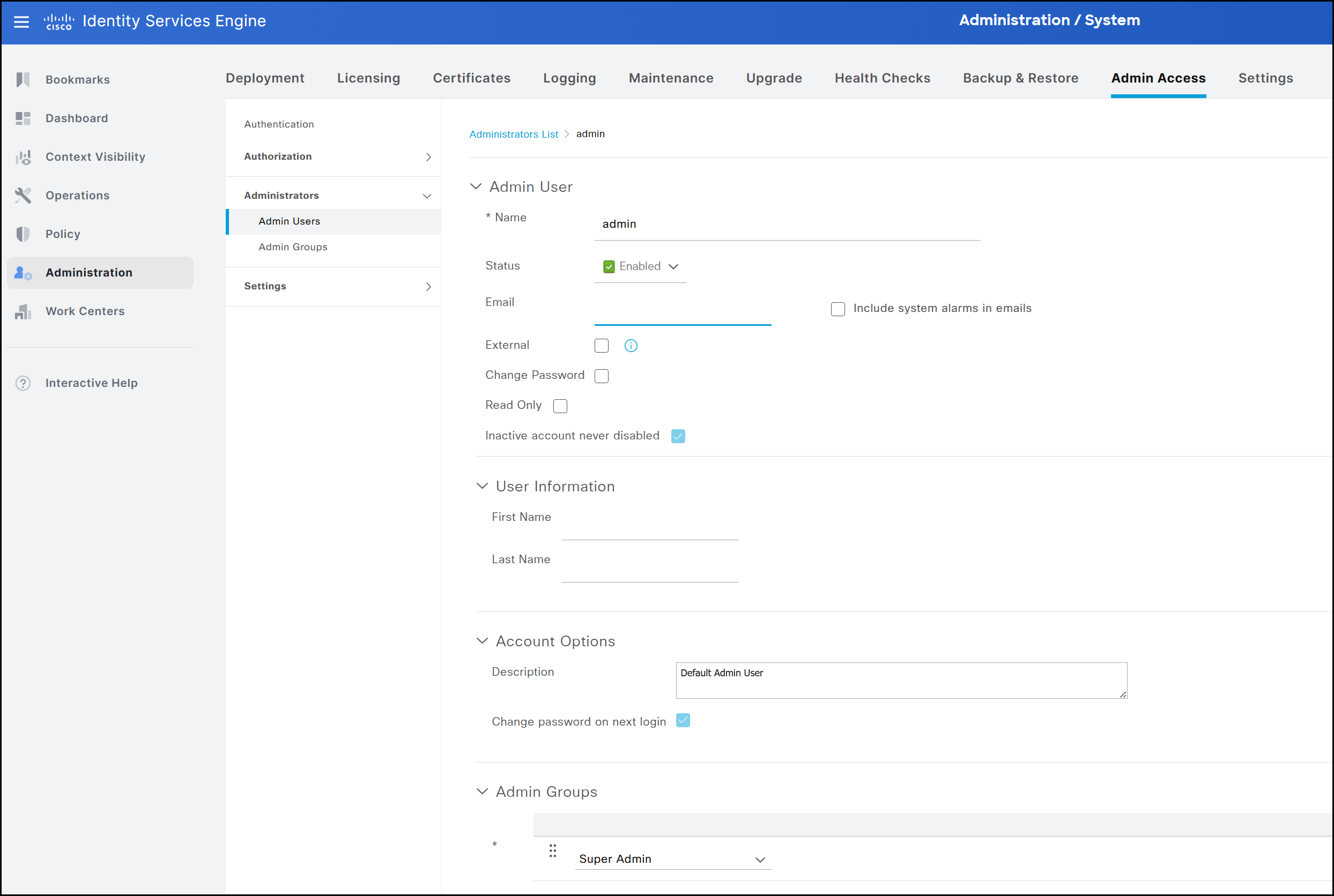
As mentioned, among these attributes, the ones that cannot be modified for the administrator (Super Admin) account created during the node setup are the following:
- Account status
- Read-only setting
- Requirement to change the password at the next login
- Administrator groups assigned to the account
GUI administrator access in ISE is governed by a Role-Based Access Control (RBAC) model, where permissions are determined by the administrator group assigned to the user. These groups may include local accounts defined within the ISE cluster or external groups, such as those defined in Active Directory. Based on group membership, ISE determines which features, pages, and information are accessible to each administrator.
In contrast to the CLI, which supports only two role types, the GUI offers a significantly broader range of administrator groups and also supports the creation of custom groups.
The image below illustrates all default groups available in the GUI.
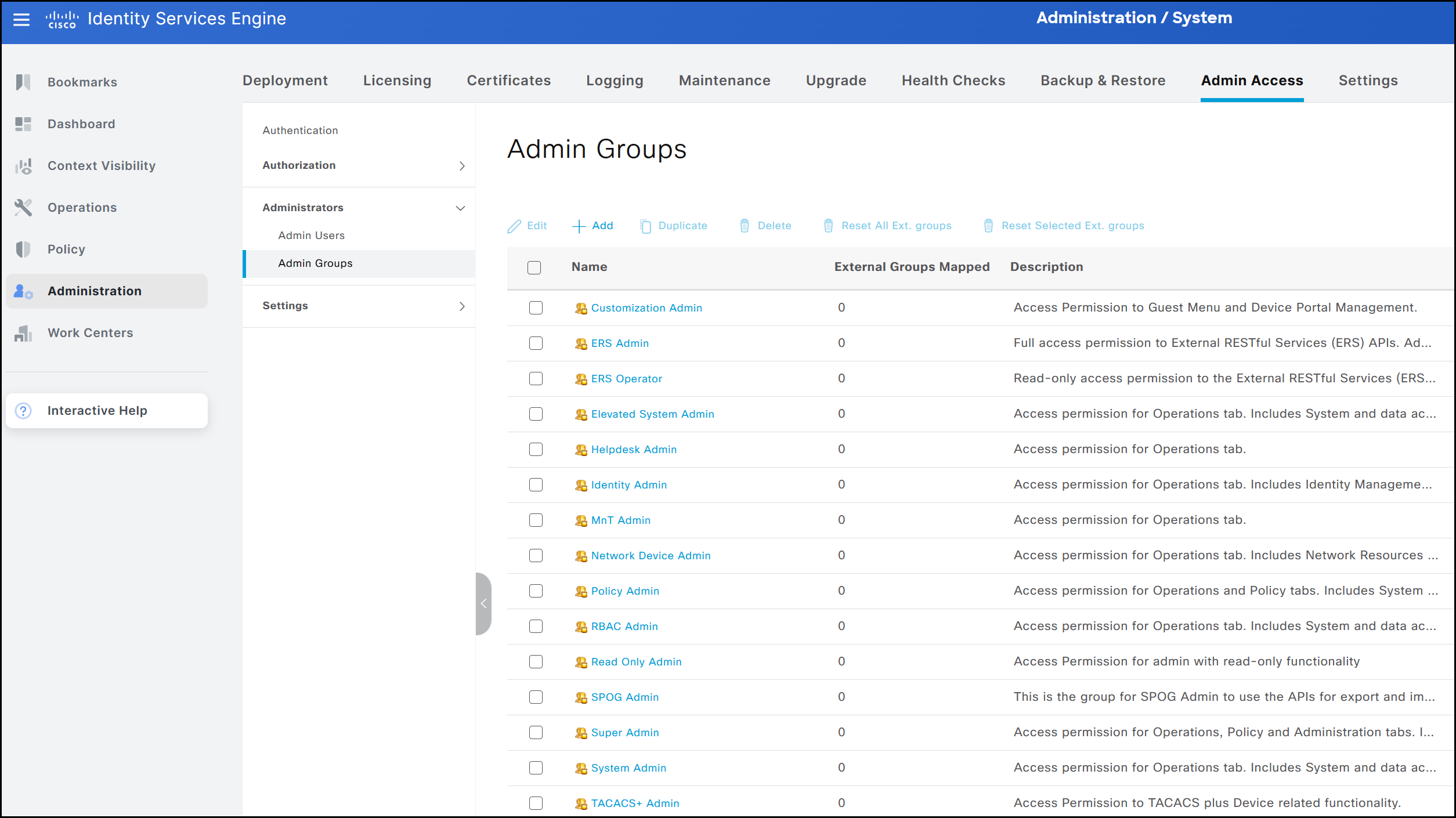
The option to create custom groups is particularly useful when there is a need to define profiles with specific levels of access or visibility. For example, a group may be configured to block access to all TACACS-related information. As a result, both the corresponding menus and data remain hidden to any user belonging to that group.
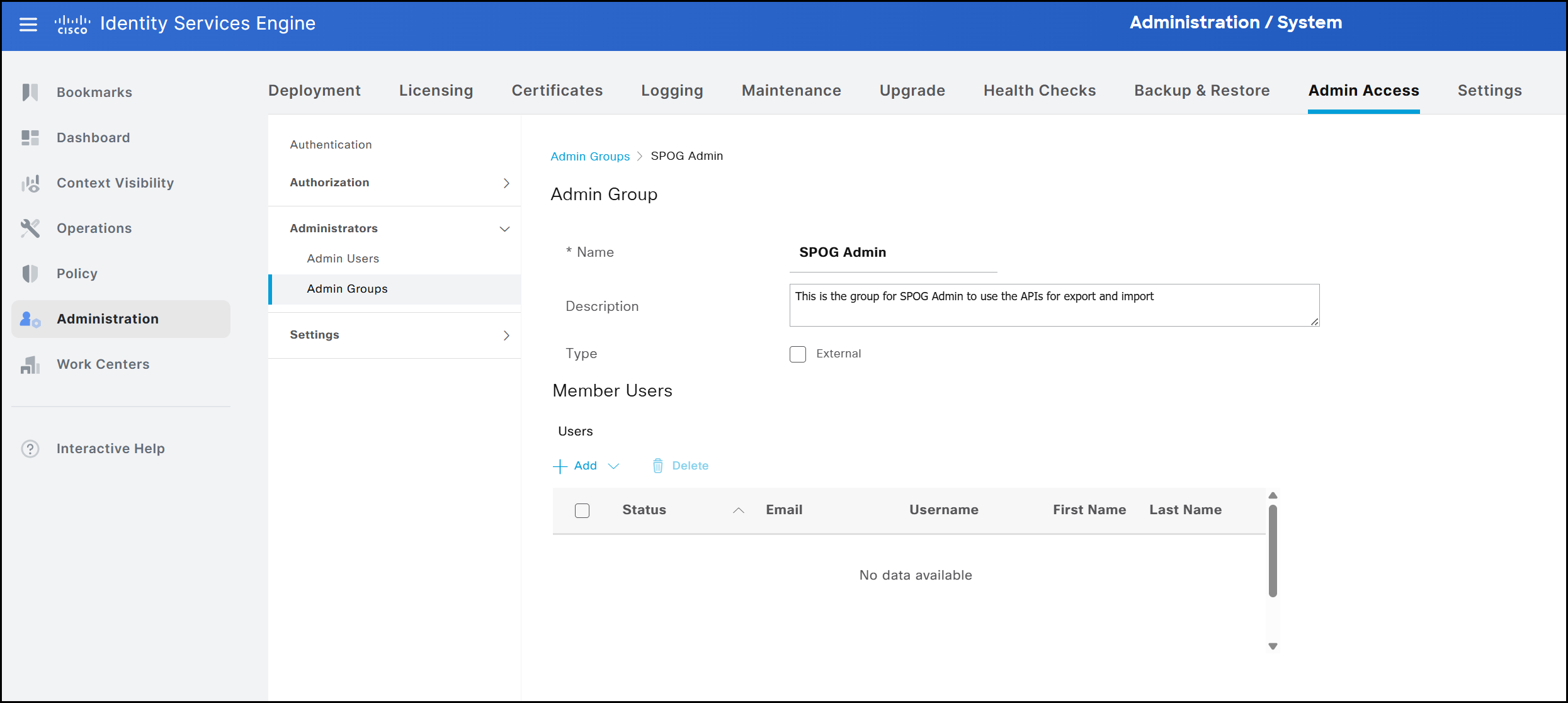
As mentioned earlier, administrator groups can be either internal or external. Internal groups consist of local administrator accounts created within ISE, whereas external groups are mapped to users who belong to groups defined in an external identity source, such as Active Directory. When a custom group is created, it is defined as internal by default. To associate it with one or more external groups, the External option must be selected and the appropriate AD groups mapped to the local group.
To better illustrate how RBAC and administrator groups interact, a temporary test group named groupTest is created. This group will be used shortly when defining the RBAC policy.
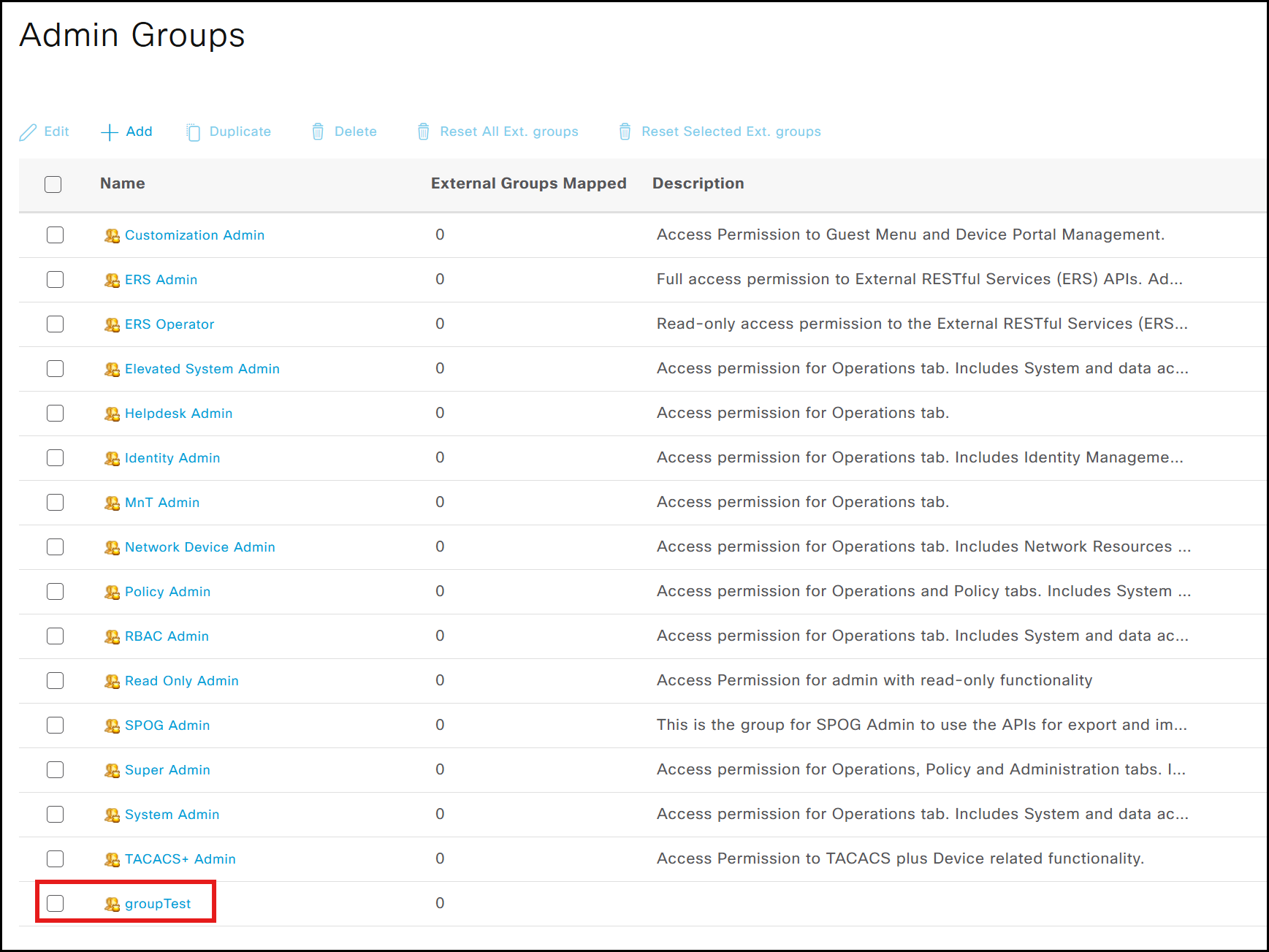
Once the group has been created, it is possible to create and associate a new user named testUserRBAC with it.
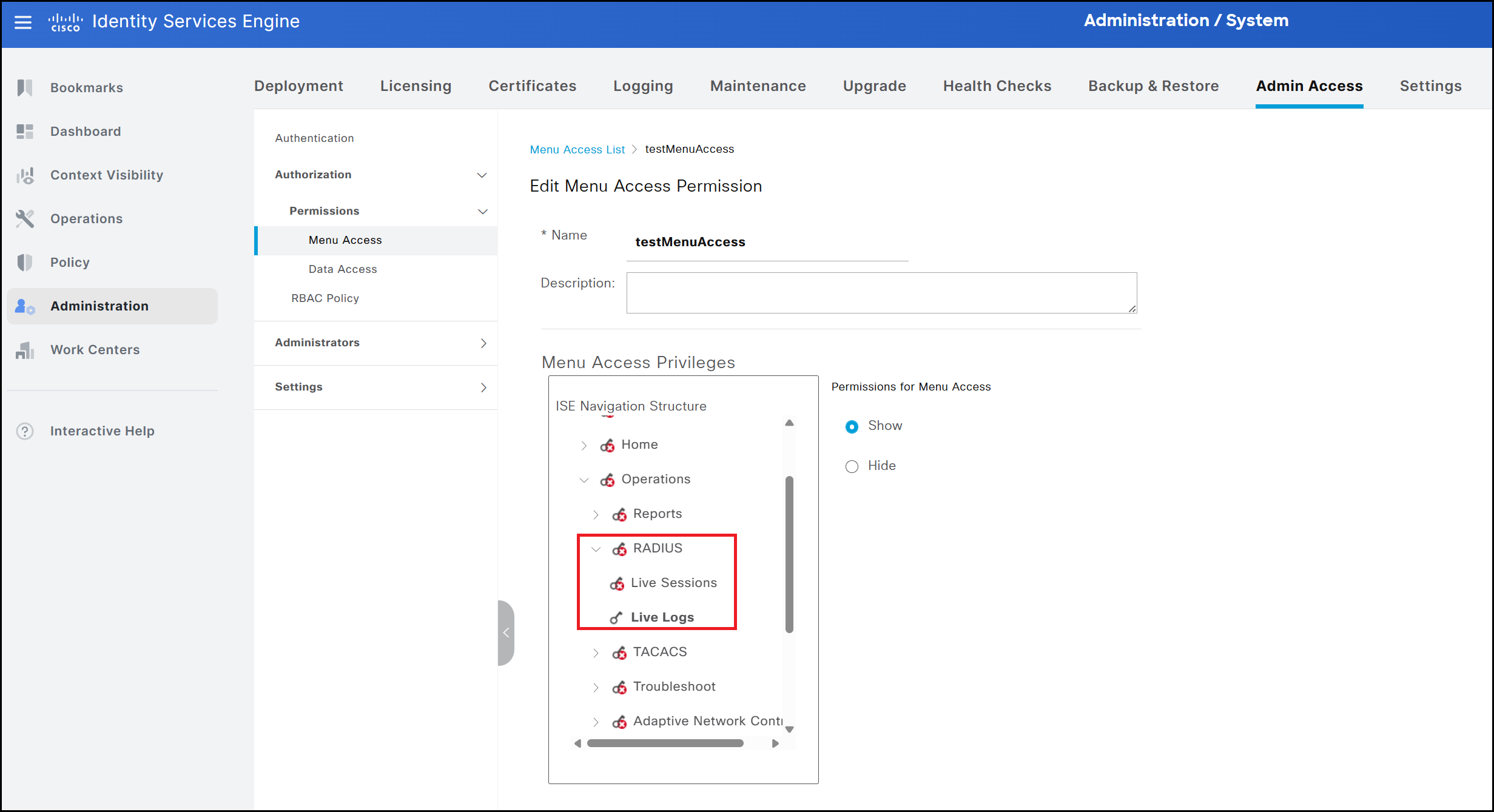
The next step is to define which resources the group is allowed to access. This process requires two components: permission objects and RBAC policies. Permission objects define which menus and data are visible in the GUI for users within a specific group, while RBAC policies, created at the final stage of the workflow, combine these permission objects and apply them to the appropriate group. ISE provides a number of default permission objects for both menu and data visibility. The Menu Access interface shown below allows administrators to specify which menus are accessible. The drop-down list mirrors the structure of the ISE GUI, and menu visibility can be controlled using the Show and Hide options.
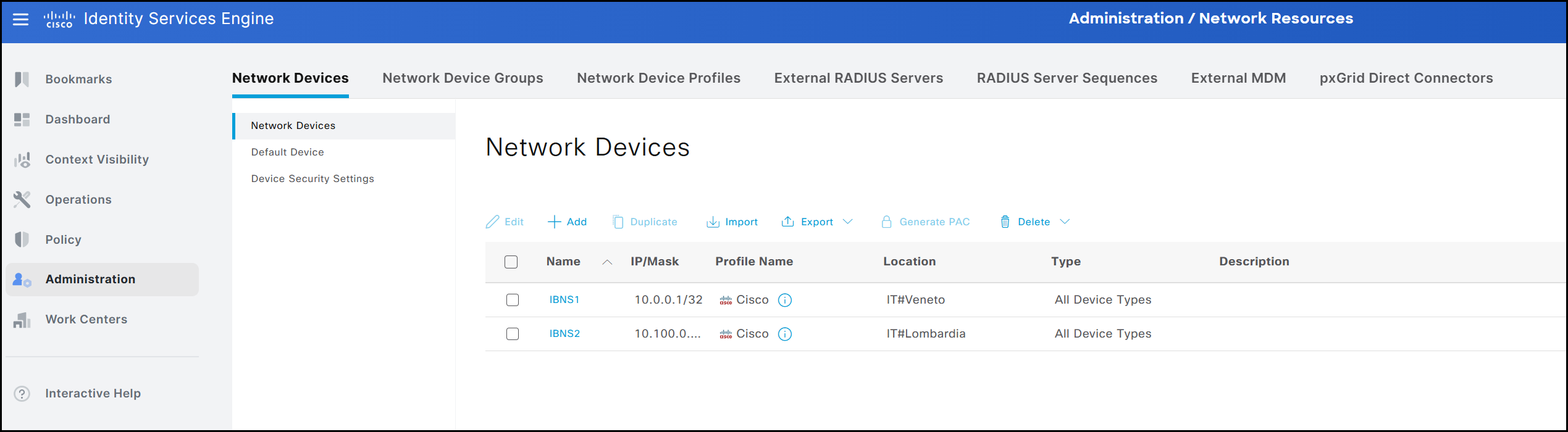
For demonstration purposes, a new permission object named testMenuAccess is created by following the path Administration → System → Admin Access → Authorization → Permissions. In this example, the user’s visibility is limited to the Network Devices page, showing only the information relevant to it.
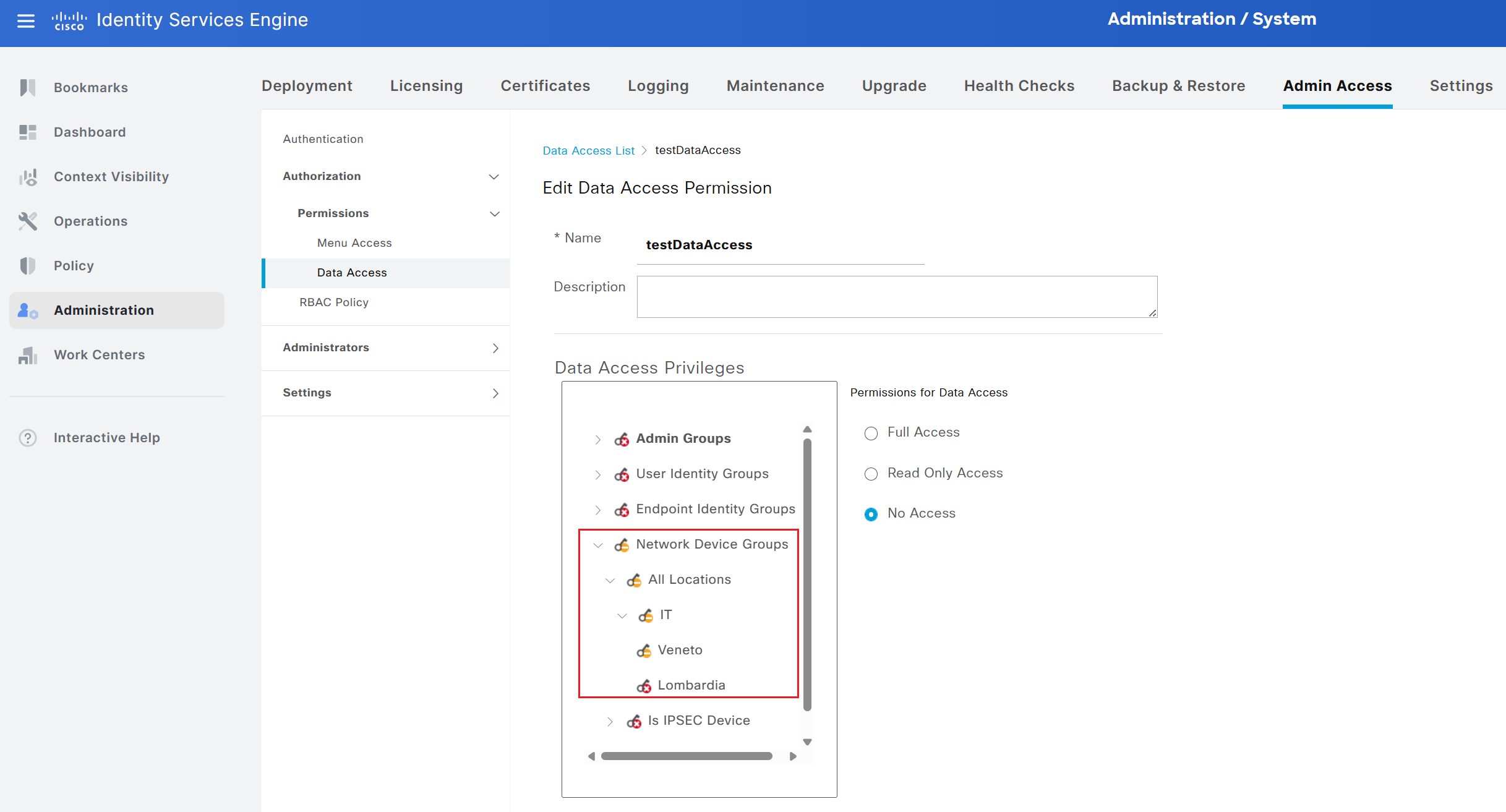
The same approach applies to data visibility through the Data Access tab. A new permission object is created by selecting Add and naming it testDataAccess. All information available in ISE can be displayed or hidden according to the visibility requirements of the selected group. In this example, only information related to network devices associated with the location All Locations → IT → Veneto is made visible.
After creating these permission objects, the final step is to combine them into an RBAC policy by entering Administration → System → Admin Access → Authorization → Permissions → RBAC Policy. RBAC policies associate a group with the defined visibility settings. As in other areas of ISE, several default RBAC policies are available and can be applied simply by assigning newly created users to the corresponding default groups. Note that the default RBAC policies cannot be modified or disabled.
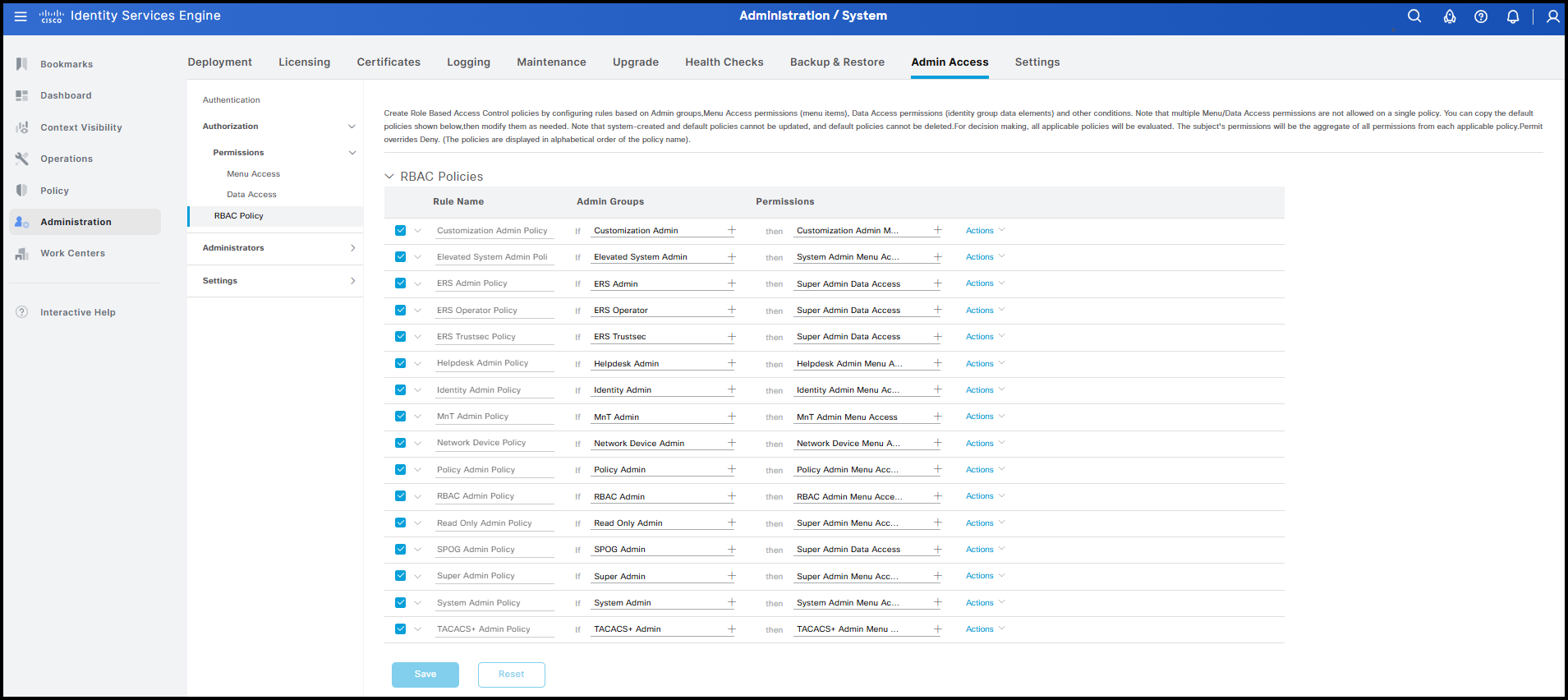
The logic behind RBAC is straightforward. For each policy, ISE checks whether a user belongs to the specified group. If the condition is met, the associated Menu Access and Data Access objects are applied to that user. To create the final policy, select Actions from any existing policy and choose Insert New Policy. Assign a name, such as RBAC Group Test Policy, and specify the group to which the policy applies, in this case groupTest. The last step is to associate the visibility settings we prepared earlier, testMenuAccess and testDataAccess.
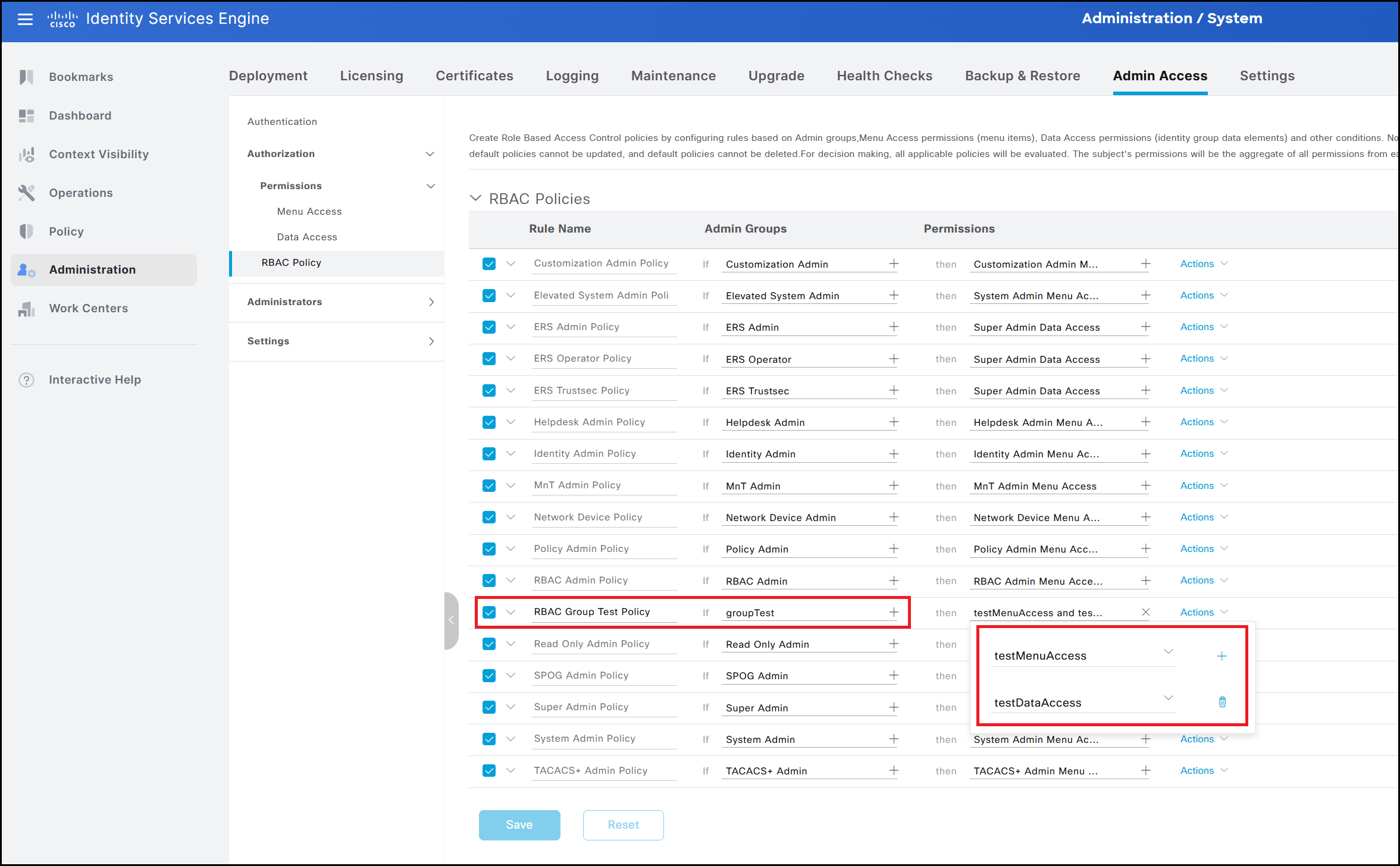
The final result is shown in the figure below. The user’s visibility is restricted according to the settings defined in the previous steps, both for menus and data. Specifically, the user can access only the interface dedicated to Network Devices. Within this interface, visibility is limited to devices associated with the IT → Veneto location, while devices associated with other locations, such as IT → Lombardia, remain hidden.
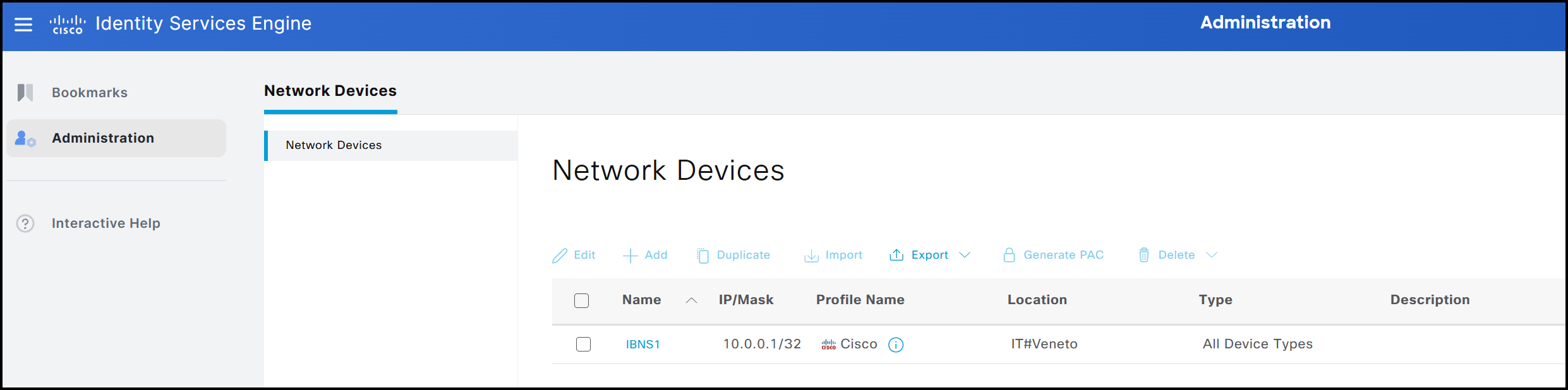
This shows the visibility of the adminstup user belonging to the Super Admin group.
GUI Account Verification
The GUI also allows viewing currently logged-in users, similar to the CLI. This information can be accessed by navigating to Administration → System → Admin Access → Settings → Session → Session Info.
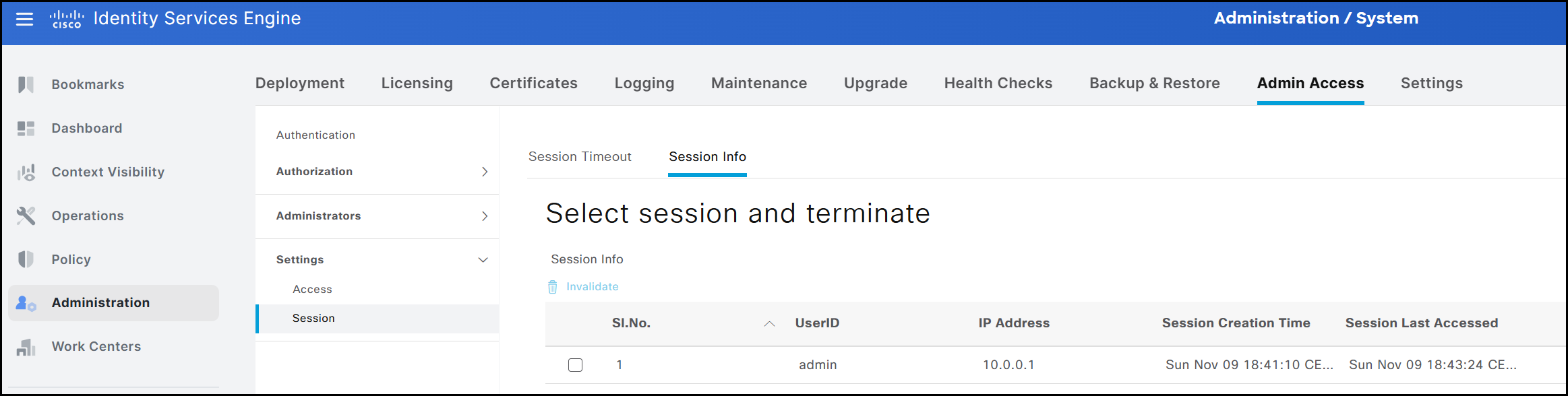
This view displays the following details:
- The username of the active session, in this example adminstup
- The IP address from which the user is connected, shown as 192.168.0.1
- The timestamp indicating when the current session was established, shown as 25 March
- The timestamp of the previously created session, shown as 25 March
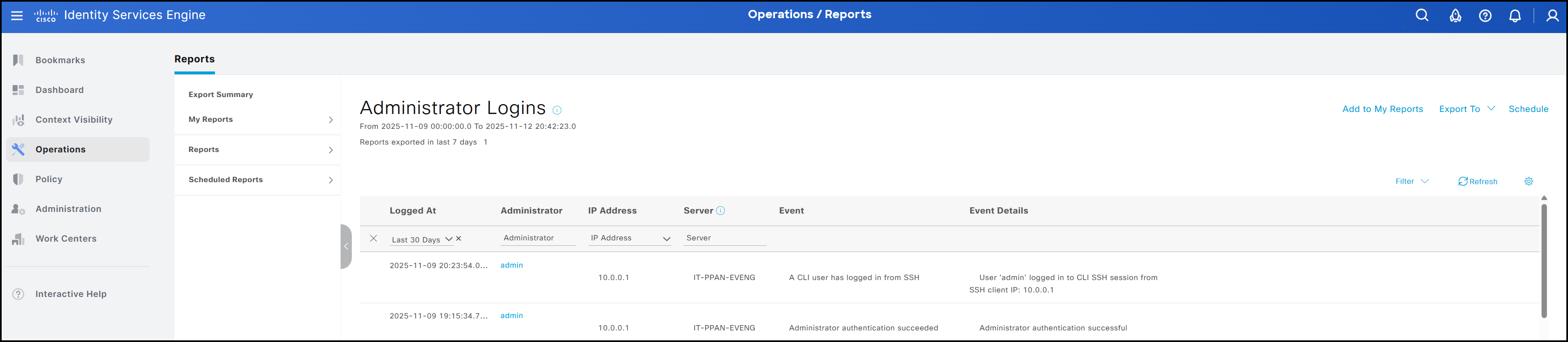
As with the CLI, the GUI also allows a Super Admin to forcibly terminate another user’s session. This can be done from the same interface shown previously in Session Info. The session to be ended can be selected on this page, and clicking Invalidate will terminate it. In addition to viewing currently active sessions, it is also possible to review the historical record of user sessions, similar to using the show logins cli command in the CLI. The figure below shows a summary. In general, both users created via the CLI and those created via the GUI are included. To access this summary, navigate to Operations → Reports → Reports → Reports → Audit → Administrator Logins.
GUI Account Password Policy
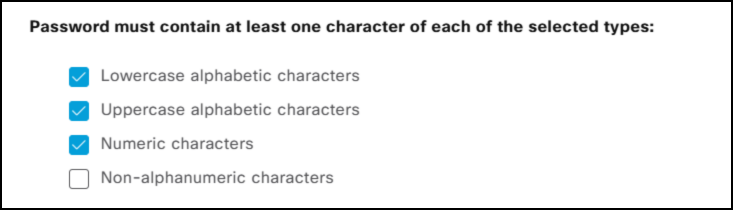
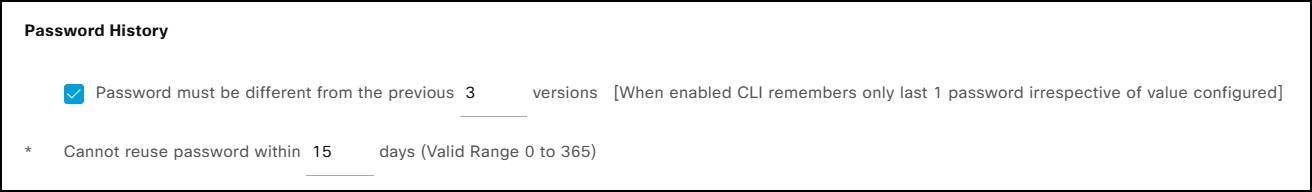
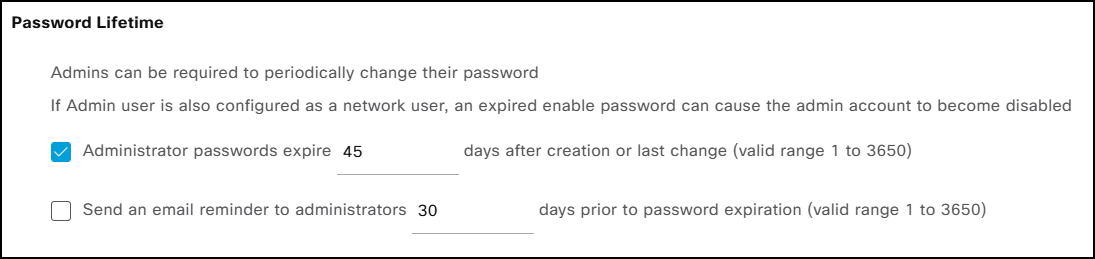
As discussed in the CLI section, password policies can only be configured through the GUI. These policies govern the composition of user passwords and are organized into five subsections within the interface:
- Password must not contain
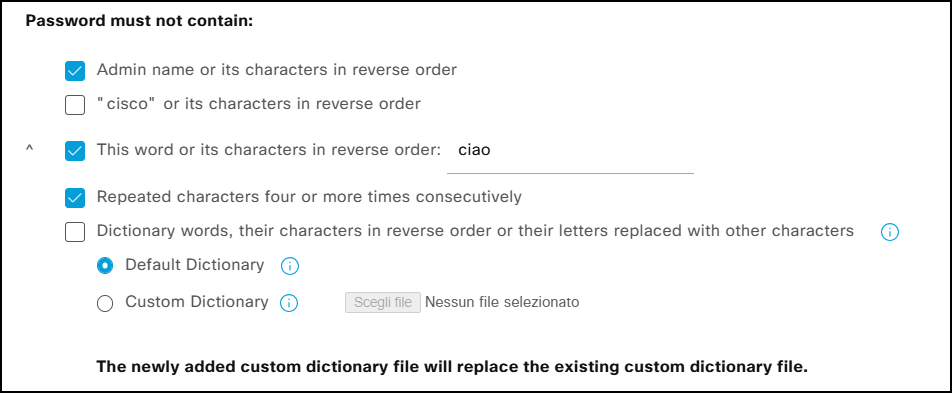
- Password must contain at least one character of each selected type
- Password History
- Password Lifetime
- Display Network Device Sensitive Data
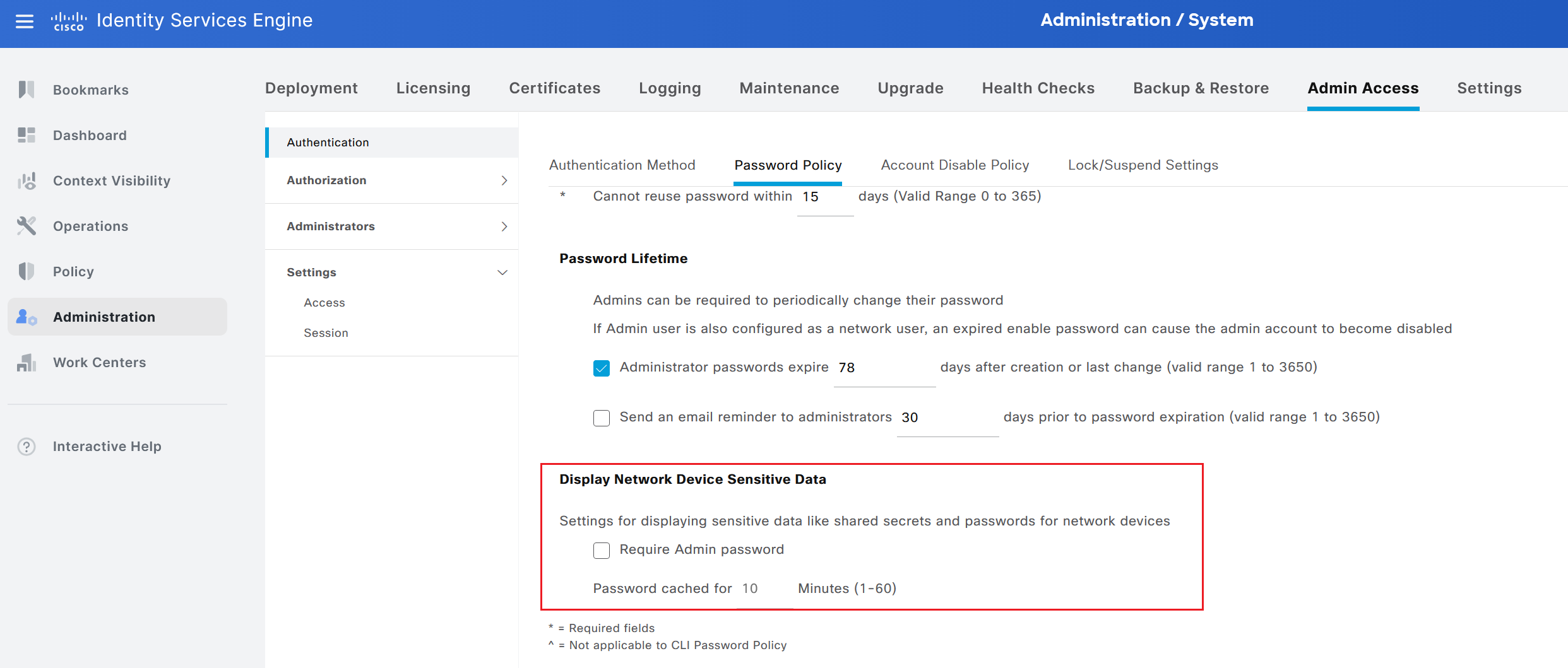
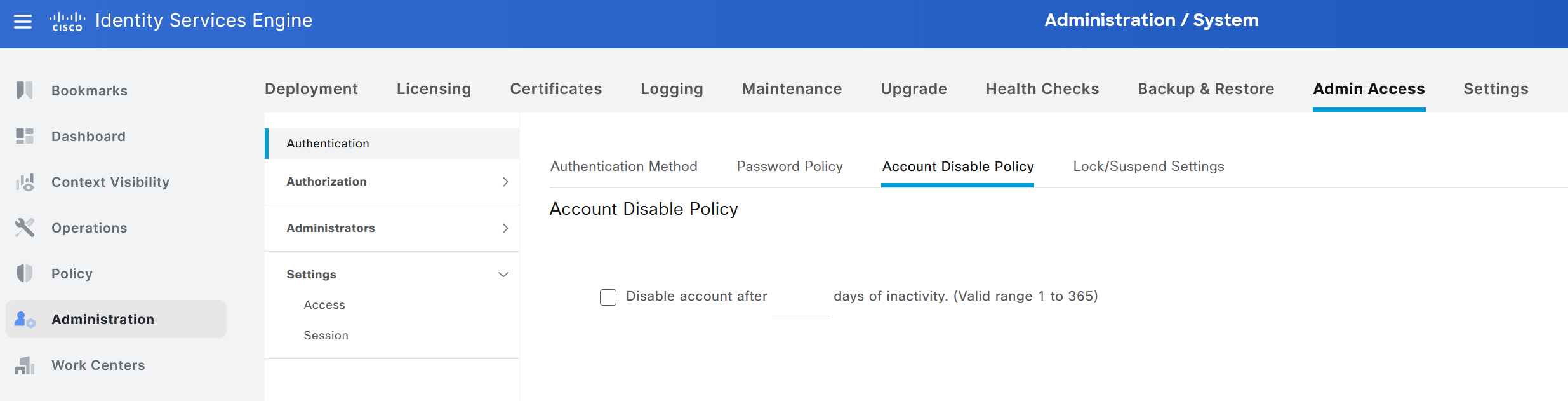
In addition, it is possible to specify the minimum password length. Configuration entries marked with the ^ symbol do not apply to CLI-created accounts. For instance, the system cannot check for the presence of a specific word (or its reverse) within a password. Beyond password policies, the GUI also allows administrators to configure account inactivity and suspension settings (same concept discussed previously). For inactivity, an account can be automatically disabled after X days, as illustrated in the figure.
Access can also be restricted for users who repeatedly enter an incorrect password, using the same configuration settings described in the CLI section. Consecutive failed login attempts can thus be managed by:
- Suspending the account for X minutes
- Locking the account, thereby rendering it disabled; to re-enable it, an administrator with the appropriate permissions must manually reactivate the account via the GUI as well
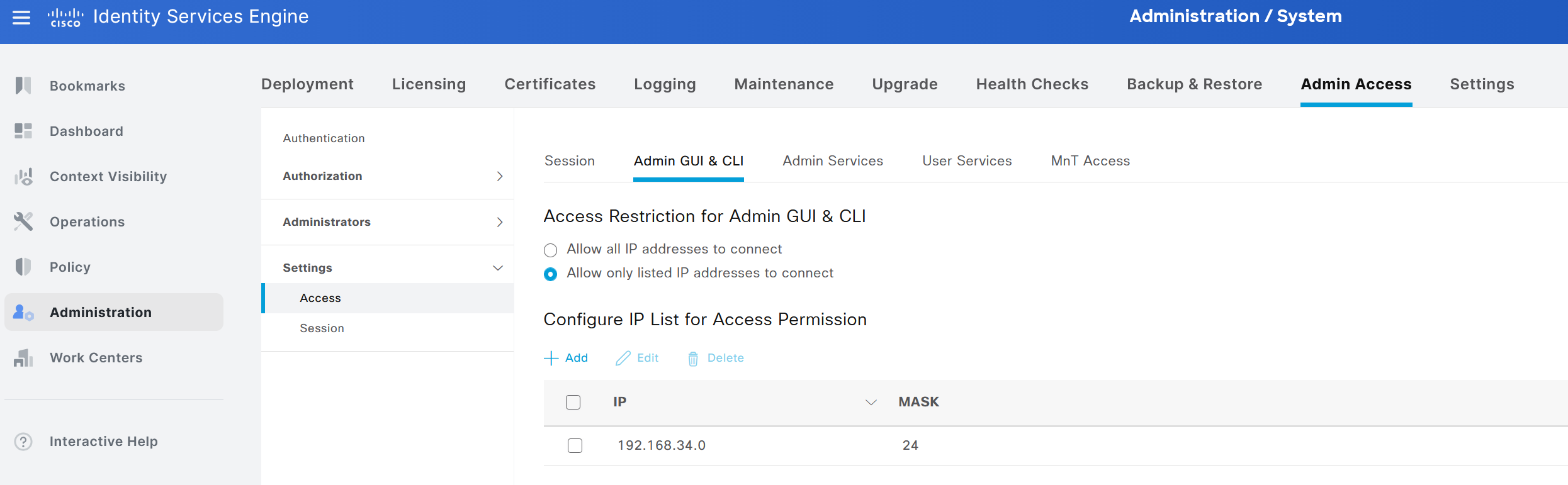
Services Access Restriction
Within ISE, it is possible to restrict access to specific IP addresses or IP ranges. Although this can be done more precisely at another point in the network, such as a firewall, it is also possible to configure this restriction directly within ISE. By default, access is permitted from all IP addresses. The interface where these settings can be defined is Administration → System → Admin Access → Settings → Access. From here, there are multiple sections where access can be restricted on an IP basis for different services.
For example, for GUI and CLI access, the configuration shown below allows requests only from the subnet 192.168.34.0/24.
Takeaways
Managing user accounts for administrative access is one of the key steps during the staging of a new ISE cluster, as it allows for the accurate definition of roles and accountability for each operational group.
In general, access to the ISE GUI is typically managed through an external identity store, such as Active Directory. It is common to associate different levels of access and visibility with these external accounts. The same approach can be applied to CLI access, allowing a single identity store to manage all user accounts.
There are also additional nuances and configuration options for GUI access, such as certificate-based authentication (although this is not widely used) or SAML authentication with MFA.
That’s all for this post. I hope you found it helpful. If you have any additional insights or questions, feel free to reach out via social media. See you in the next one!

